───✱*.。:。✱*.:。✧*.。✰*.:。✧*.。:。*.。✱ ───
Recently, one of my professors fell victim to malware through a malicious link. I was curious, so he sent me the link and I did a small analysis with my little knowledge in malware.
This post is for educational purposes only, do not attempt to reconstruct this malware or use it for any malicious purposes.
Target
This malware targets people through Discord, and it aims to sell Discord accounts, as well as to steal information such as browser passwords, browser cookies, and cryptocurrency wallets.
Malware Analysis
The website of the malware is hosted via Netlify, which has now been taken down. However, I was able to get a small snapshot of the website while it was still up.

The website was relatively unsuspecting, it looks like a normal website for an indie game. However, the download button links to a malicious executable hosted within Dropbox.
Downloading the Malware
If you download the malware, it immediately starts scraping your files for browser passwords, browser cookies, and cryptocurrency wallets.
I was able to scrape together pieces of the source code of the malware, and I was able to identify that it searches the following directories for credentials:
%APPDATA%\discord\%APPDATA%\discordcanary\%APPDATA%\discordptb\%APPDATA%\discorddevelopment\%APPDATA%\lightcord\%LOCALAPPDATA%\Google\Chrome\User Data\Default\%LOCALAPPDATA%\BraveSoftware\Brave-Browser\User Data\Default\%LOCALAPPDATA%\Yandex\YandexBrowser\User Data\Default\%LOCALAPPDATA%\Microsoft\Edge\User Data\Default\%APPDATA%\Opera Software\Opera GX Stable\%APPDATA%\Opera Software\Opera Stable\%APPDATA%\Roaming\Exodus\
In the source code, it also searches for specific browser extension settings, which will store information such as secret keys for cryptocurrency wallets like MetaMask.
- MetaMask
- Exodus
- Zerion
- Phantom
- Coinbase
- Rabby
- Keplr
- Magic_Eden
- Ronin
- Trust
Reverse Engineering the Malware
This malware was pretty poorly written, so it was relatively easy to reverse engineer.
Since I knew it would target Discord users, I decided to use the strings command to find strings in the malware binary, piped into a grep command to search for the word “discord” (which I hoped would be something like a Discord token stealer, or something related).
strings rasiel.exe | grep -i -n "discord"After running the command, it spit out a long string that looked like obfuscated JavaScript code.
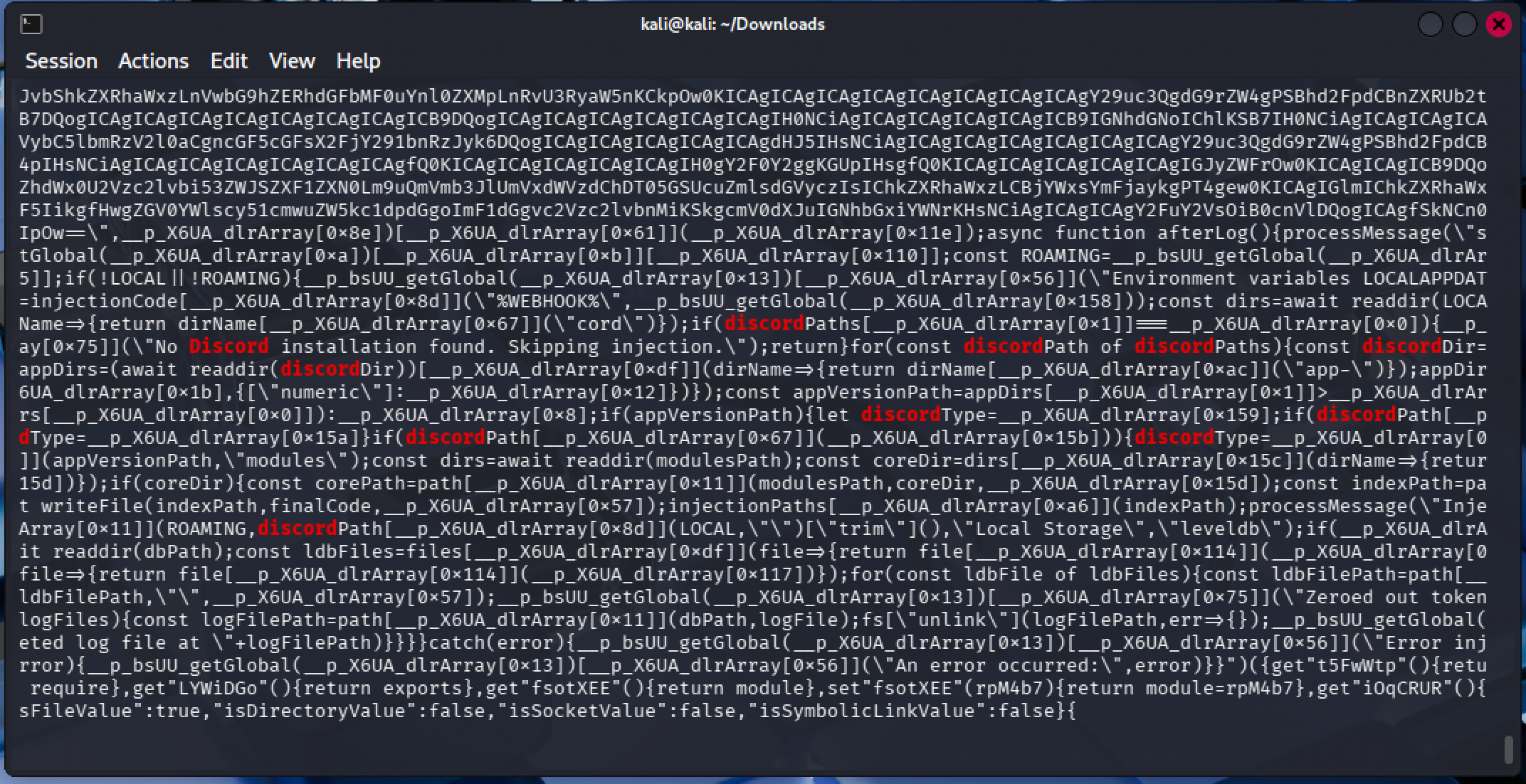
After a bit of deobfuscation with webcrack, I was able to get the original source code. I will NOT be providing this source code, as it would be irresponsible to share code that could be directly reused for malicious purposes.
Nuking Their Webhook
Once I had the original source, I was able to identify that they were exfiltrating data to a Discord webhook. So, I wrote a little Python script to send this message, every second, to their webhook.
This was an attempt to get them to remove the webhook, which would effectively be a “kill switch” for the malware to send the stolen information to their Discord server. I also thought that if their channel with stolen credentials was spammed with a bunch of garbage, it would make it harder to find the actual credentials sent before my spamming. This isn’t super effective, as they can purge the channel somehow, but I thought it would be annoying enough to get them to remove the webhook.
This worked, after sending this message every second for about 2 hours, it returned a 404 error, indicating that the webhook was removed.
Unfortunately, they replaced the malware with a newer .exe file, which had another webhook URL that I also nuked.
Interesting Finds
Within their source code, there were a few interesting Turkish strings that I found to be a little funny. It also had a “VM check”, but it was never actually ran, so I’m not really sure what it was for.
For instance, once it finds that you have a cryptocurrency wallet, it sends “wallet dustu omg” (“wallet found omg”) as well as “anani sikeyim wallet oha” (“I’ll f*ck your mother wallet, wow”).
It also had a check for “high quality friends”; it would check your Discord friend list for other users with things that are deemed as high quality, such as having certain badges or having an account age that was more than a few years old.
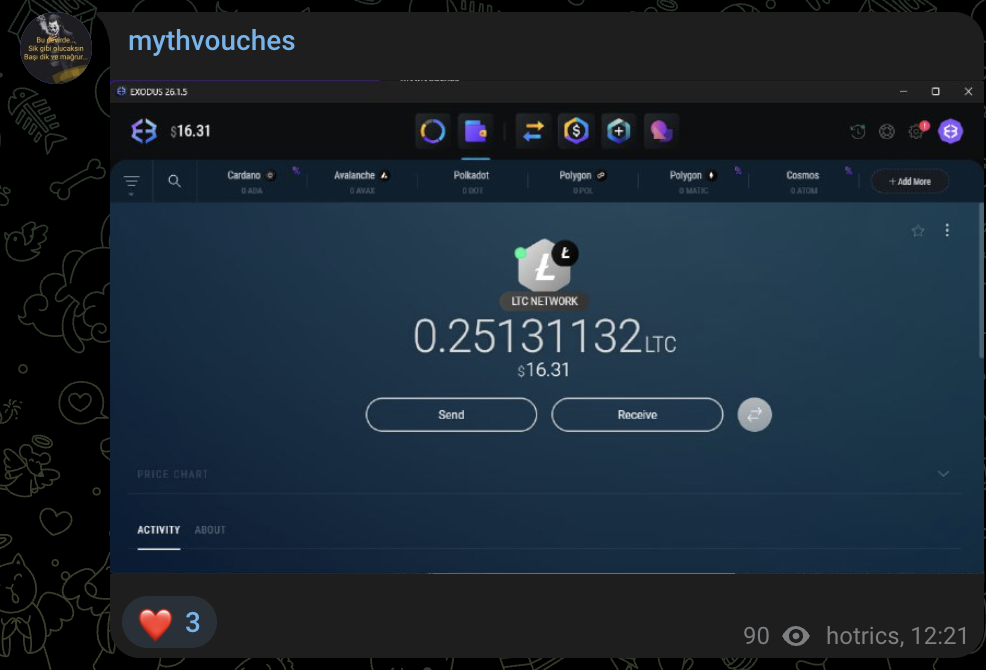
In their source code, they also advertised their Telegram channel, which I was able to join and see a few messages from them. For instance, they were bragging about their accounts that they stole, and their crypto wallets with $17 worth of LiteCoin.
Conclusion
Don’t click random links sent from people on Discord, even if they claim to be testing a game. If you think you might have clicked something suspicious, treat your accounts and devices as compromised, and change your passwords. Also, make sure to enable two-factor authentication on all of your accounts when possible, as this will help prevent unauthorized access to your accounts.
In security, there are three authentication factors: something you know (such as a password), something you have (like a phone with two-factor authentication), and something you are (like a fingerprint or facial recognition). Using multiple types together is the best form of authentication, as it provides a layer of defense against unauthorized access to your accounts.
───✱*.。:。✱*.:。✧*.。✰*.:。✧*.。:。*.。✱ ───